Let’s implement an SSL/TLS certificate to secure Apache. Once the certificate has been implemented, HTTPS access to the configured domain/IP will be possible.
Let’s get it started. We will, at a high level, carry out the following.
- SSL module compilation for Apache HTTP 2.4.5
- Get SSL Certificate
- Configure Apache for SSL support
Install SSL Support for Apache from Source
Apache HTTP must be compiled with mod ssl to configure SSL. I’ll show using a CentOS 7 VM from Digital Ocean.
- Log in as root to the Linux server and download the most recent version of Apache
wget http://www-us.apache.org/dist//httpd/httpd-2.4.25.tar.gz .- Using the gunzip command
gunzip -c httpd-2.4.25.tar.gz | tar xvf -- There will be a new folder named “httpd-2.4.25.”
- Execute the following configure command inside:
./configure --enable-ssl –-enable-soNote: If you are performing this task on a brand-new server, you may encounter APR, PCRE, and OpenSSL-related issues; consult the troubleshooting guide for more information.
Ensure that you did not receive any errors from the above configure command, and then install using make instructions.
make
make installAs usual, ensure there are no errors in the preceding commands. This determines that an Apache web server with SSL functionality has been deployed.
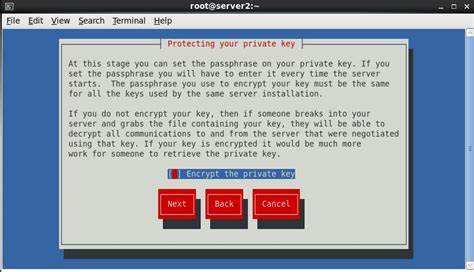
Obtaining a Secure Sockets Layer (SSL) Certificate
There are various ways to generate and obtain the certificate authority’s signature on an SSL certificate. If you wish to establish SSL on the Intranet web server, the majority of organizations have an internal certificate issuance team that you must contact. However, you must still generate a CSR (Certificate Signing Request), which you can do with OpenSSL.
If you wish to secure an Internet-facing URL, you can purchase a certificate from VeriSign, GoDaddy, Namecheap, ZeroSSL or you can obtain a free certificate from Let’s Encrypt.
Let’s Encrypt is a collaboration project of the Linux Foundation that offers a free SSL/TLS certificate. Let’s Encrypt will be used to acquire a certificate for my domain – Chandan.io. There are various ways to produce a CSR, but I’ve found that the “SSL For FREE” web application is the simplest.
- Enter the URL you wish to protect.
- Download your domain certificate files after verifying domain ownership using one of the given ways.
- You will receive three configuration files for the Apache web server.
- This is your key file, which should not be distributed publicly.
- Certificate – your actual SSL certificate
- Ca bundle – Signer root/intermediate certificate
- Transfer the file to the Web Server. We will require them soon.
Configuring Apache SSL
And as a final step, Apache must be configured to serve the request over HTTPS.
- Connect to the Apache webserver.
- Create a copy of the httpd.conf file (located by default at /usr/local/apache2/conf/).
- Open the file with the vi editor and verify that the mod ssl module and httpd-ssl.conf are there and uncommented.
LoadModule ssl_module modules/mod_ssl.so
Include conf/extra/httpd-ssl.confWe’ll configure the certificate details using the httpd-ssl.conf file. There are a number of conditions that must be met to ensure that the parameter exists.
- SSLCertificateFile – The path of the Certificate CRT file that was downloaded before.
- SSLCertificateKeyFile – private.a key file path
- SSLCertificateChainFile — Location of the ca bundle.crt file
(Create a new folder and name it “ssl” to store all certificate-related files.)
- If necessary, create a backup and use the vi editor to alter the file.
SSLCertificateFile "/usr/local/apache2/conf/ssl/certificate.crt"
SSLCertificateChainFile "/usr/local/apache2/conf/ssl/ca_bundle.crt"
SSLCertificateKeyFile "/usr/local/apache2/conf/ssl/private.key"You must configure the “ServerName” directive next. Typically, it is your domain or URL.
ServerName chandan.io- Save the file and restart Apache
cd /usr/local/apache2/bin
./apachectl stop
./apachectl startLastly, confirm that your domain is mapped to the newly configured web server IP. Once complete, attempt HTTPS access to your website. As can be seen, Chandan.io is accessible via https using the certificate I specified.
The aforementioned procedures are important for installing an SSL certificate, and you must further harden and secure the SSL, as described here. You may also wish to test your web server’s SSL/TLS before going live to ensure it is not vulnerable to typical security flaws. I hope this provides you with a sense of how to implement an SSL certificate on your Apache Web server so that URLs are accessible through HTTPS.