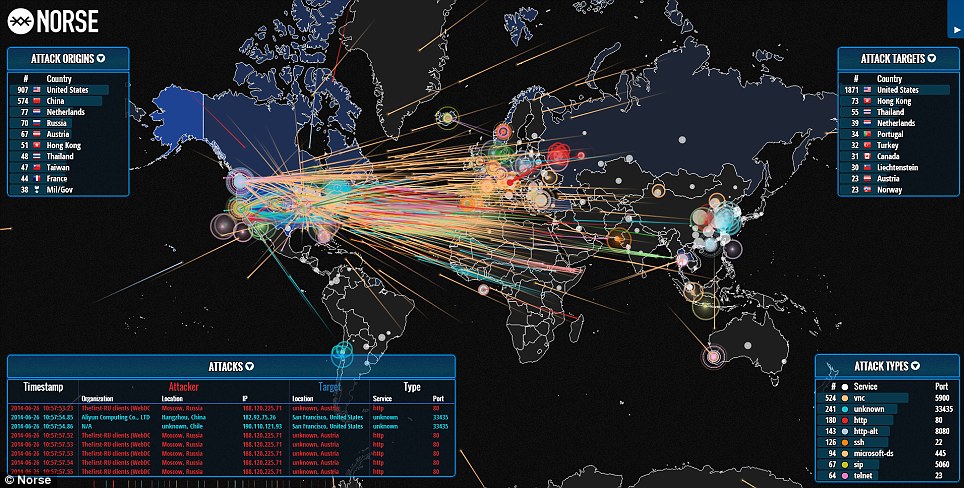
Globally, it is fascinating to observe who initiates cyberattacks against whom. Every day, thousands of websites are hacked owing to insecure server configurations, plugins, and files. If you are the owner or administrator of a website, you can execute a security scan to check for vulnerabilities and viruses. This article lists down some of the best tools to view cyberattack maps.
11 Ways to View Real-Time Cyberattack Maps – Live Hacking Attack
Returning to the article, if you are interested in tracking global attacks, the following maps will captivate you.
1. Digital Attack Map

Watch daily DDoS attacks worldwide with Digital Map of Attack. You can filter the map with multiple options.
By attacks size
- Large
- Unusual
- Combined
By attack type
- TCP Connection (filling connections)
- Volumetric (eating bandwidth)
- Fragmentation (pieces of packets)
- Application
- Source & destination port number
- Duration
DDoS is hazardous to your internet business, since it can bring down your online presence and harm your profits and reputation. If you are a business owner or web administrator, you may want to safeguard your online assets from DDoS using SUCURI or one of the other services described in this article.
2. FireEye Cyber Threat Map

Using the above information, the FireEye Cyber Threat Map provides an outstanding snapshot of the total number of attacks occurring today.
- Top 5 industries reported
- Top attacker by nation
It is less extensive than the one above, but still valuable if you are seeking for industry and country-specific statistics.
3. Kaspersky – Tools to View Cyberattack Maps

Kaspersky’s Cyberthreat real-time map displays the real-time attacks identified by their various source systems.
- On-Scanner access
- On-Demand Scanner
- Web Anti-virus
- Mail Anti-virus
- Intrusion Detection System
- Vulnerability Scan
- Kaspersky Anti-spam
- Botnet Activity detection
You can include tabular data on the statistics page.
4. Threat Cloud

Check Point’s Threat Cloud displays attack statistics for today and yesterday. It also provides the opportunity to view the leading source and target nations.
5. AKAMAI – Tools to View Cyberattack Maps

Real-time web monitoring by AKAMAI provides an overview of network and attack traffic, which may be filtered by geography.
6. Threatbutt

Threatbutt’s Internet assault attribution map is a cool and basic one. You are able to view live attack details, including source and target information, when the program is utilized to launch an attack.
7. FortiGuard – Tools to View Cyberattack Maps

FortiGuard’s real-time threat intelligence landscape. More than 2 million Fortinet products worldwide generate data. You receive an overview of the attack, including its origin and severity.
8. Bitdefender

Bitdefender’s Cyberthreat map depicts three primary categories of assaults.
- Spam
- Infection
- Attack
Bitdefender is an industry leader in the distribution of home and commercial security products.
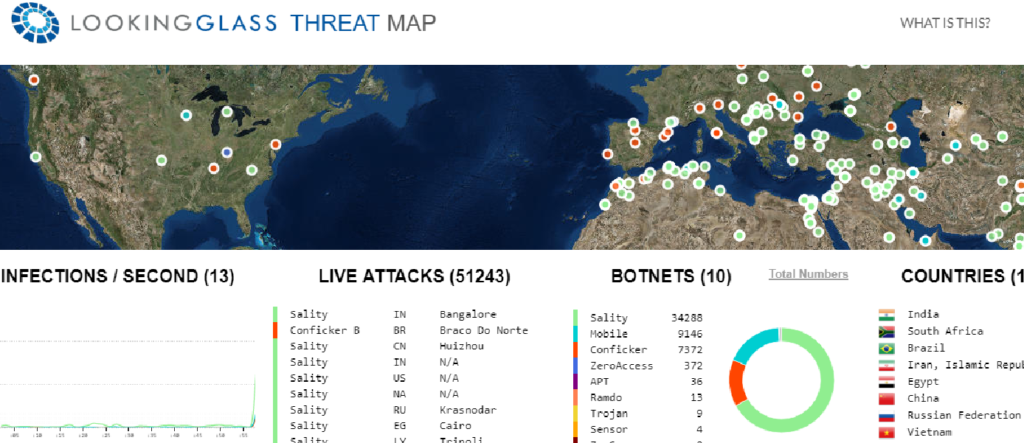
9. LookingGlass
Cyveillance’s real-time data stream reveals infection records and harmful and phishing URLs. In addition to the live attacks and infections per second, the botnet operations are also displayed.
10. Talos

Talos, a subsidiary of Cisco, possesses a cyber-attack map that depicts the leading spam and malware senders. Globally, data is collected from Cisco and third-party feeds. You may view the top ten senders of malware and spam, along with their volume and nation.
11. Netscout

The Cyber Threat Horizon report by Netscout. Global DDoS occurrences in real time. You can filter the data by bandwidth, source, destination, event category, and event type (UDP, IPv4, DNS amplification) (Amplification, Volumetric, TCP connection). Netscout publishes a global DDoS summary as well.
Conclusion
Did you enjoyed the real-time cyberattack maps? It’s crazy. Isn’t it? So make sure to give these a try.